How Insurance Companies Build a 7-Year, Audit-Ready Communication Record
Within the communication architecture, insurers need to be compliant across SMS, email, WhatsApp, voice, and in-app channels. How are some insurers compliant while others are struggling?
TLDR
IRDAI requires 5 to 8 years of communication retention, but most insurers cannot produce a complete record under audit pressure because logs are scattered across vendor dashboards, CRM modules, and deprecated aggregator systems. The failure is not on the sending side; it is on the retrieval side. Fixing it requires a central orchestration layer that tags every message with policy context at the point of send, syncs logs to insurer-owned storage, and maintains an unbroken audit trail across vendor migrations, channel changes, and partner workspaces.
Why Does an IRDAI Audit Create a Communication Crisis for Most Insurers?
Picture this. Your IRDAI auditor arrives and requests a complete communication history for Policy #LI789456, covering January 2019 to present. The policy has had two renewal cycles, one endorsement, and a partial claim settlement.
Your IT team starts pulling the record. The WhatsApp Business logs from your current provider only go back 90 days. The SMS records from the period of 2019 – 2021 live in a deprecated aggregator system that your team stopped using after a vendor switch. Email archives require manual CSV exports from a third-party platform. The claim intimation communications are in your CRM's activity log, but the CRM does not store the actual message content, only that a message was triggered. Push notifications exist in a separate analytics dashboard that does not expose individual message history.
Three weeks later, your team has a partial record with gaps across two vendor transitions. The auditor flags the gaps. What should have been a routine inspection becomes an extended review.
This is not an unusual scenario. It is the default outcome for any insurer that has grown its communication infrastructure organically, adding and replacing vendors, channels, and partners over time without a unified record-keeping layer in the middle.
IRDAI's Master Circular mandates a minimum of five years of retention for policy-related documentation from the date of maturity or settlement, extending to eight years for unit-linked plans, long-term health policies, and policies with ongoing claims.
The DPDP Act creates additional obligations on top: insurers must demonstrate explicit consent, purpose limitation, and a complete communication history for any data subject access request.
Regulators have also moved beyond accepting policy documents that describe compliance controls. They now request evidence from specific transactions, specific customers, and specific dates.
An insurer that cannot produce a complete cross-channel communication history within hours of an audit request has a compliance gap, regardless of how thorough its written procedures are. In ombudsman proceedings, inability to produce evidence of proper notification has resulted in judgments against insurers in mis-selling allegations, claim denial disputes, and premium revision cases.
The problem is not that records were never created. The problem is that they were created in the wrong places.
Fyno was built to address these exact gaps.
What Are the 5 Operational Purposes a 7-Year Audit Trail Serves?
Most compliance discussions focus narrowly on satisfying IRDAI documentation requests. A well-designed audit trail does much more than that. It serves five distinct operational purposes, and a communication infrastructure that addresses only the first one will fail the other four.
1. Regulatory Compliance and Rapid Evidence Production
The most immediate purpose: producing complete, accurate, timestamped communication records for IRDAI inspections, DPDP data subject access requests, and consumer court proceedings. The standard is not just "records exist"; it is "records are accessible, complete, and searchable within hours."
2. Fraud Detection and Insider Threat Visibility
Centralized communication logs allow fraud and security teams to detect anomalous patterns: unusual volumes of notifications from a specific underwriter, claim-related messages triggered outside normal approval chains, or communication sent to phone numbers that were not registered on the policy at the time of send. Without a unified audit log, these patterns are invisible because each vendor's data exists in isolation.
3. Claims Dispute Resolution and E&O Liability Reduction
When a policyholder disputes a premium revision or claims they were never notified of a policy lapse, the communication record becomes the primary defense for the insurer. Errors and omissions (E&O) liability exposure is directly correlated with the quality of communication documentation. A complete audit trail showing the exact message sent, the approved template version used, the delivery confirmation received, and the timestamp relative to the policy event, can resolve disputes before they escalate to ombudsman level.
4. Operational Integrity and Maker-Checker Accountability
Insurance communication is not just customer-facing messaging. It involves internal governance: who approved a template change, when, and why. Who triggered a claims communication above a certain threshold? Which underwriter initiated a policy modification that required a customer notification? A 7-year audit trail captures the governance chain behind every message, not just the message itself. This is critical for demonstrating effective internal controls during regulatory reviews.
5. Customer Experience Documentation and Fair Treatment Evidence
IRDAI's conduct-of-business expectations increasingly focus on fair treatment of policyholders. Communication records serve as evidence that insurers disclosed risks, communicated charges, explained claim decisions, and responded to complaints in a timely and accurate manner. During any investigation into mis-selling or unfair treatment, the communication trail is the primary documentary evidence.
What Must Every Insurance Communication Audit Trail Actually Capture?
A complete audit record is not just a delivery log. For IRDAI and DPDP purposes, every communication event needs to carry the following elements:
So, where is the gap today?
The gap that most insurers discover too late is that the standard vendor platforms capture delivery logs. They do not capture policy context, approval chains, or template version history. Those live in other systems. And no system ties them together automatically.
Why Do Traditional Systems Fail When Auditors Come Asking?
How Does CPaaS Retention Architecture Create Auditing Gaps?
Standard CPaaS retention windows run 30 to 90 days, after which records are archived to cheaper storage with limited searchability. The search interfaces these platforms provide are designed for operational troubleshooting — finding a failed delivery from last Tuesday, not producing a five-year policy lifecycle record by policy number.
When an insurer migrates from one WhatsApp Business provider to another, the historical conversation record stays in the old system. If contract access expires before the migration is complete, those records may be permanently inaccessible. No CPaaS platform connects message logs to policy context: the log shows that a message was sent to a phone number, not that it was a claim intimation for a specific policy triggered by a specific adjuster under a specific approval.
Why Does CRM-Native Messaging Leave Evidence Gaps?
CRMs log that a communication event occurred, but they rarely store the actual message content, the delivery confirmation, or the template version used. Marketing teams modifying email templates within a CRM typically have no approval workflow and no version control trail. Changes go live without a compliance review. SMS and WhatsApp communications handled through CRM integrations exist in a third-party system with its own retention policy, one that is often invisible to the insurer's compliance team.
What Does Multi-Vendor Fragmentation Look Like at Audit Time?
A typical Tier-2 insurer routes SMS through one provider, WhatsApp through another, email through a third, and push through a fourth. Each vendor maintains separate logs, separate retention windows, and separate export interfaces. Reconstructing a complete cross-channel journey for a single policy requires manual coordination with each vendor, CSV consolidation in Excel, and timeline alignment, all under audit deadline pressure.
A policyholder who received an SMS premium reminder, did not respond, received a WhatsApp follow-up two days later, clicked a payment link, and then received a confirmation email. That complete sequence exists across three separate vendor dashboards with no shared identifier connecting the records. For IRDAI purposes, none of those individual records is sufficient. The complete journey along with delivery confirmation for each step, is what auditors need.
How Does Fyno's Orchestration Architecture Fix Each of These Gaps?
The architectural answer to the audit retrieval problem is not a better log-management tool layered on top of fragmented systems. It is a vendor-neutral orchestration layer that sits above all CPaaS providers and channels, capturing the complete communication record at the point of send — before the message touches any downstream vendor.
This is precisely how Fyno's communication orchestration platform works for insurers. Here is how each gap closes.
Gap 1: CPaaS 30-to-90-Day Retention Window
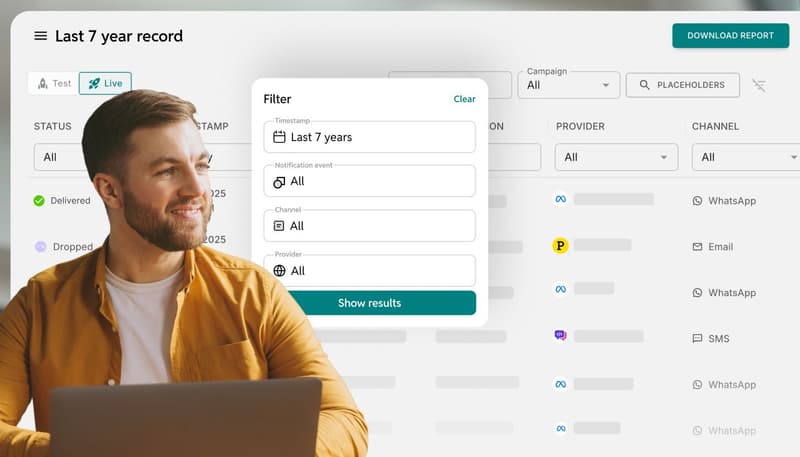
Fyno's unified logs interface captures every outbound communication at the orchestration layer — before it touches the downstream CPaaS provider. This means the retention clock is governed by Fyno's storage architecture, not by Gupshup's or Sinch's dashboard.
Every message event is written to Fyno's immutable log with the full payload: exact message content, recipient details, channel used, vendor routed through, delivery confirmation status, and precise timestamp. That record is simultaneously synced to insurer-owned infrastructure — S3 buckets or Azure Blob Storage, using append-only storage with cryptographic hashing for tamper evidence.
The insurer's authoritative audit copy exists independently of whether the CPaaS vendor retains anything. A vendor switch or contract termination does not create a gap in the record because the record was never held by the vendor in the first place.
Gap 2: CRM Logs Capture Events — Not Message Content
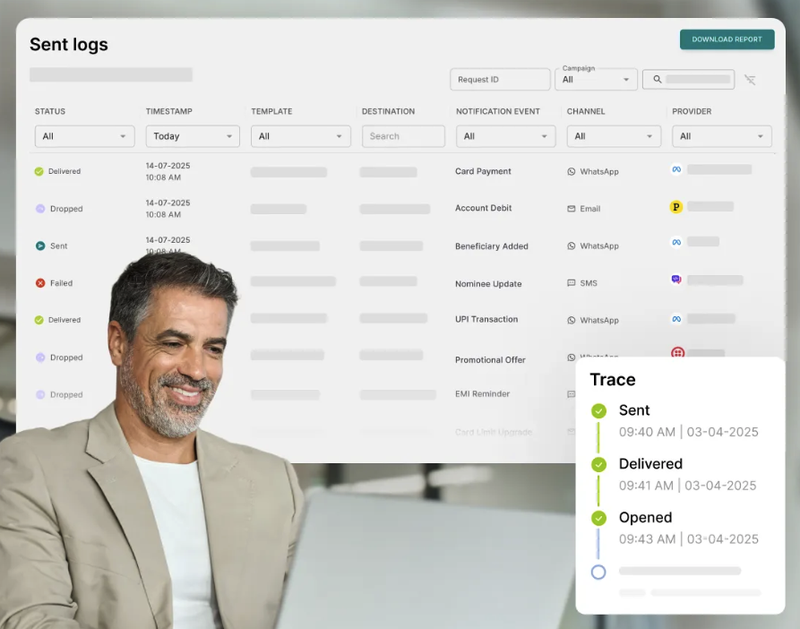
Where a CRM activity log records "premium reminder triggered," Fyno Logs captures the full message payload at point-of-send: the exact message text with all variables populated as delivered. Not just the template with placeholders, but the complete communication as the customer received it.
For a premium revision notification, the Fyno log entry reads:
"Dear Mr. Sharma, your premium for Policy LI789456 has been revised from ₹15,000 to ₹18,500 effective 1 April 2024. This change was made following your sum insured enhancement request dated 14 March 2024."
That specificity is what distinguishes an audit-ready record from an operational log. When a policyholder disputes the revision in an ombudsman proceeding, the exact message is available, not an activity timestamp.
Fyno Logs also captures the DLT template ID that was active at the time of send, the carrier delivery receipt (DLR), and the routing decision log showing which channel and vendor handled the message. The compliance team retrieves all of this from a single search interface without contacting a vendor.
Gap 3: No Shared Identifier Across Multi-Vendor Stacks
Every communication event that flows through Fyno Workflows is tagged at origination with a business context identifier that travels through the entire delivery chain: policy number, claim ID, customer lifecycle stage, business unit. This context is captured in Fyno Logs against a unified customer identifier — not against a phone number.
When an IRDAI auditor requests the complete communication history for Policy LI789456, a single search in Fyno Logs returns every SMS, WhatsApp message, email, and push notification sent under that policy number; across every vendor, across every channel, across the full policy lifecycle — sorted chronologically, with delivery confirmation for each event. There is no CSV export, no vendor coordination, no manual timeline reconstruction. A policy number returns a complete multi-year cross-channel history in seconds.
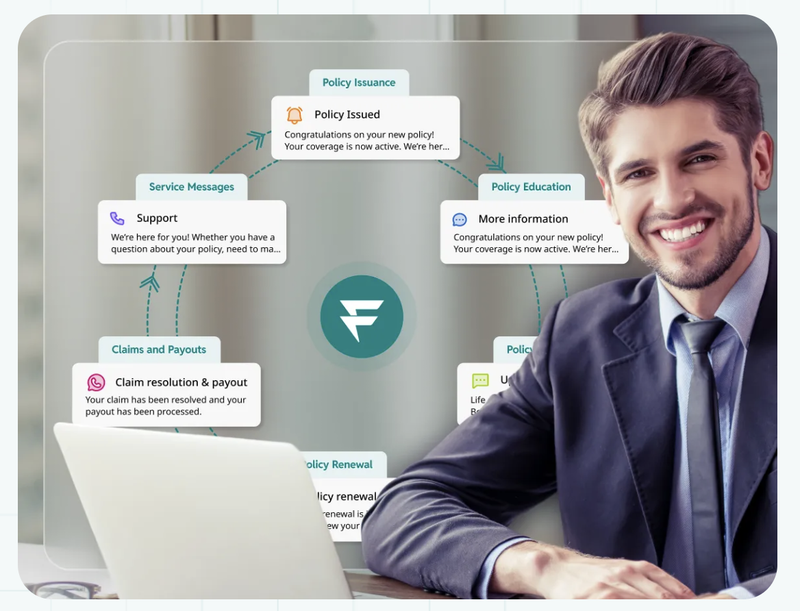
Fyno also integrates with core insurance systems — policy administration platforms, claims management systems, Finacle, Flexcube — via API or Kafka event stream. When the policy admin system fires a POLICY_RENEWAL_DUE event, Fyno Workflows receives it, selects the correct template, routes through the appropriate channel based on consent preferences, executes the delivery, and writes the full event context to the audit log — all without engineering involvement in the communication layer.
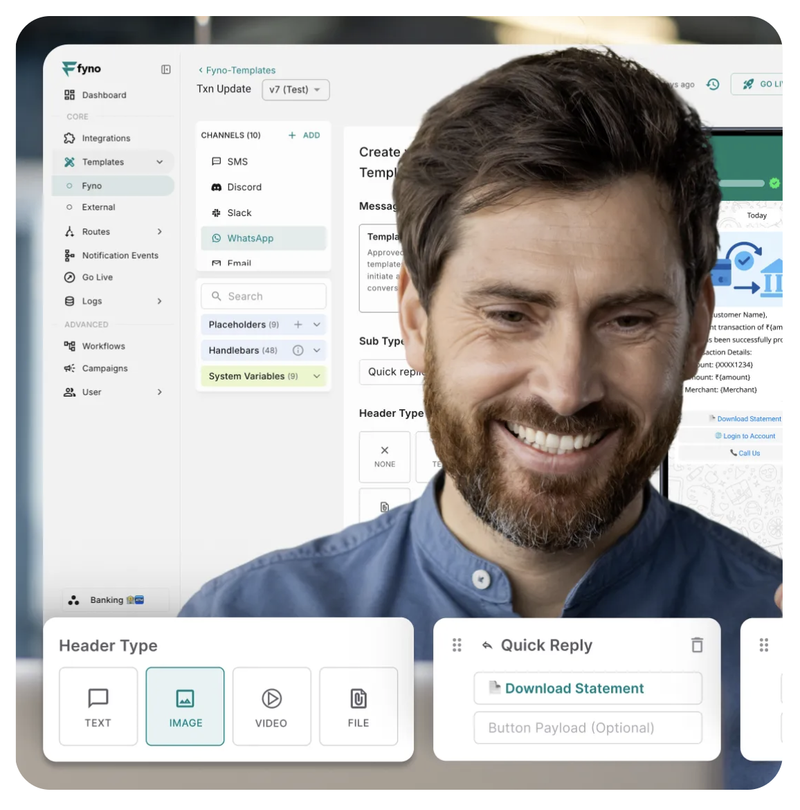
Gap 4: Template Changes With No Version History or Approval Chain
Fyno's template management system creates a version-controlled record of every template change: who modified it, when, what the previous version contained, and whether the change was approved before it went live.
Maker-checker enforcement is built in. A marketing team member drafts a template change. A compliance reviewer receives an in-app and email notification and approves or rejects with a recorded reason. Only then does the template go live. Every action in that chain is logged with user identity and timestamp.
Critically, the version history captures the full content of every version — not just that a change was made. If an auditor asks which version of the premium revision template was active on a specific date in 2022, Fyno returns the exact template text that was live at that date, the diff from the previous version, the identity of the approver, and the DLT registration ID that was mapped to that version. For SMS, DLT registration is managed within the same system with bi-directional sync to TRAI's DLT platforms — making TRAI's November 2025 variable pre-tagging requirements auditable at the template level without any separate record-keeping.
Gap 5: Claims Workflow Context Is Not Embedded in Message Logs
Fyno Workflows connects to claims management systems via event triggers. When a claims adjuster closes a settlement above a defined threshold, that approval action triggers a Fyno workflow that selects the approved communication template for that claims stage, populates it with the claim-specific variables, routes through the appropriate channel based on the customer's consent preferences, and writes the complete event to Fyno Logs.
The log entry does not say "notification sent." It says: claims settlement notification sent for Claim ID CL-2024-8834, settlement amount ₹3.2L, triggered by the adjuster approval event at 11:38 IST, message delivered via WhatsApp to the registered number at 11:39 IST, delivery confirmed. The approval chain — who triggered the event, under what authorization — is embedded in the message log, not stored separately in a system an auditor must cross-reference.
Each stage of the policy lifecycle generates the same level of audit-grade context: proposal received, underwriting decision, policy issued, renewal reminder, lapse notice, claims intimation, survey scheduled, approval granted, payment processed. Every stage is documented with the business event that caused it and the communication that resulted.
Gap 6: Partner and Bancassurance Workspace Isolation
Fyno Connect supports multi-tenancy workspace architecture for bancassurance partners, broker networks, and OEM distribution channels. Each partner operates in an isolated workspace with its own analytics and operational view. The central insurance compliance team sees an aggregated audit trail across all distribution channels — without exposing one partner's data to another.
This directly addresses the IRDAI requirement to demonstrate governance across all distribution channels while maintaining the data isolation that IRDAI's confidentiality regulations require between insurer and intermediary.
Build In-House vs. Purpose-Built CCM Platform: Which Makes Sense for Insurers?
Building audit-grade communication infrastructure in-house requires 12 to 18 months and sustained engineering investment. Vendor API instability, DLT operator-specific logic, and edge cases around mid-policy phone number changes or delivery failures during maintenance windows generate ongoing development work.
Build in-house if the migration cost and disruption risk may outweigh the benefits of switching.Or if your regulatory requirements extend significantly beyond standard IRDAI and DPDP obligations.
Choose a purpose-built platform if you need audit readiness within 90 days, your engineering bandwidth should focus on underwriting, claims, and customer portal innovation, vendor flexibility matters operationally, or you have bancassurance, broker, or OEM partner workspace requirements where centralized compliance oversight is non-negotiable.
For most Tier-1 and Tier-2 insurers, the total cost of ownership over three years is lower with a purpose-built platform and the audit risk during a build period is a risk that an IRDAI inspection can expose at any time.
What Should Insurance IT and Compliance Teams Do Now?
The audit cycle is not a hypothetical future event. Every insurer processing 50,000 or more policies annually will face documentation requests from routine compliance reviews, consumer complaints, ombudsman proceedings, or regulatory investigations. The preparedness gap is an operational decision, not a compliance project to be deferred.
Three things to address before the next audit request arrives:
1. Map your current communication record gaps. For each channel and vendor in your stack, identify the actual retention window, the search capability (can you query by policy number across seven years?), and the status of records from any vendor migrations in the past seven years.
2. Audit your template governance chain. Can you produce, for any template currently in use, a complete version history showing every change made, who approved each change, and when? If the answer involves navigating multiple systems, the audit trail is incomplete.
3. Assess your vendor migration exposure. If you switched SMS or WhatsApp vendors in the past three years, where do the historical records from the old vendor currently sit — and is your access to that data contractually guaranteed?
Fyno's multi-channel orchestration platform is designed specifically for the retrieval challenge: a policy number returns a complete seven-year communication history in seconds, every template change carries a documented approval chain, and switching vendors does not create a gap in the record.
KEY TAKEAWAYS
IRDAI mandates 5 to 8 years of communication retention, but the real challenge is retrieval speed and completeness — not storage capacity
Audit trails serve five distinct operational purposes: regulatory compliance, fraud detection, claims dispute resolution, operational integrity, and customer experience documentation
CPaaS vendors retain logs for 30–90 days; vendor migrations create permanent historical gaps without an orchestration layer
Every audit-ready record must include exact message content, delivery confirmation, policy context, template version, and approval chain — not just a delivery status
Fyno Logs captures the complete message payload at the orchestration layer before it reaches the CPaaS vendor — the authoritative copy exists independently of vendor retention policies
Fyno Templates records full content diffs per version, approver identity, timestamps, and DLT registration mapping — every template change is auditable to a specific date
Fyno Workflows embeds policy and claims context in the message log at the point of origination — not stored separately in a system auditors must cross-reference manually
Purpose-built orchestration platforms deliver audit readiness in 8 to 12 weeks; in-house builds take 12 to 18 months and carry significant audit exposure during the build period
Fyno is an enterprise communication orchestration platform purpose-built for BFSI organizations. Fyno holds ISO 27001, SOC 2 Type II, and GDPR certifications, and is aligned with DPDP Act and RBI communication guidelines.
Frequently Asked Questions
Q: How long must insurance companies retain customer communications under IRDAI regulations?
IRDAI's Master Circular requires a minimum of five years from the date of maturity or settlement. For unit-linked plans, long-term health policies, and policies with ongoing claims, this extends to eight years. DPDP Act obligations require demonstrating consent and communication purpose throughout the data lifecycle. The practical recommendation for most insurers is seven years post-policy expiry — this covers most regulatory scenarios and supports legal dispute timelines without over-retaining beyond practical necessity.
Q: What happens if an insurer cannot produce a communication history during an IRDAI audit?
Incomplete audit trails result in regulatory penalties, extended audit timelines, and increased scrutiny in future inspections. In ombudsman proceedings, inability to produce evidence of proper customer notification has resulted in judgments against insurers in mis-selling and claim denial cases. The financial exposure from a single ombudsman judgment that could have been defended with a complete communication record often exceeds the cost of building proper audit infrastructure.
Q: Can we store communication logs in our own infrastructure rather than in vendor systems?
Yes — and for IRDAI audit purposes, this is the preferred architecture. Insurer-owned S3 buckets or Azure Blob Storage provide vendor-neutral long-term retention that survives vendor migrations and contract terminations. Compliance teams have direct access without API rate limits or vendor intermediation. Fyno automatically syncs message logs to customer-owned storage while maintaining operational dashboards on platform infrastructure, so the insurer holds the authoritative copy from day one.
Q: How do we maintain audit trail continuity when switching communication vendors?
Vendor migrations create historical data gaps unless a vendor-neutral orchestration layer maintains the central record. With Fyno, switching from one WhatsApp provider to another is invisible to the audit trail: the orchestration layer captures every communication regardless of which downstream provider delivers it, so the complete history survives the transition. Without this layer, the insurer must negotiate historical data extraction from the outgoing vendor before contract termination — an often time-constrained and incomplete process.
Q: What is the difference between operational message logs and audit-ready communication records?
Operational logs serve troubleshooting: 30 to 90 day retention, searchable by phone number, focused on recent delivery failures. Audit-ready records serve compliance evidence: seven-year retention, searchable by policy number and claim ID, capturing exact message content, policy context, approval workflows, template versions, and delivery confirmation. Operational logs prove messages are being sent. Audit records prove the right messages, with the right content, under proper authorization, reached the right customers at the right time — and that every governance step in the chain was followed.
Comments
Your comment has been submitted